SECURE DATA SHARING, DONE PROPERLY
Stop sending files.
Start using Data Vaults.
Securely share sensitive information without losing control, creating duplicate versions, or relying on unsecured file transfers.
Keep data in one place. Control access. Maintain visibility.
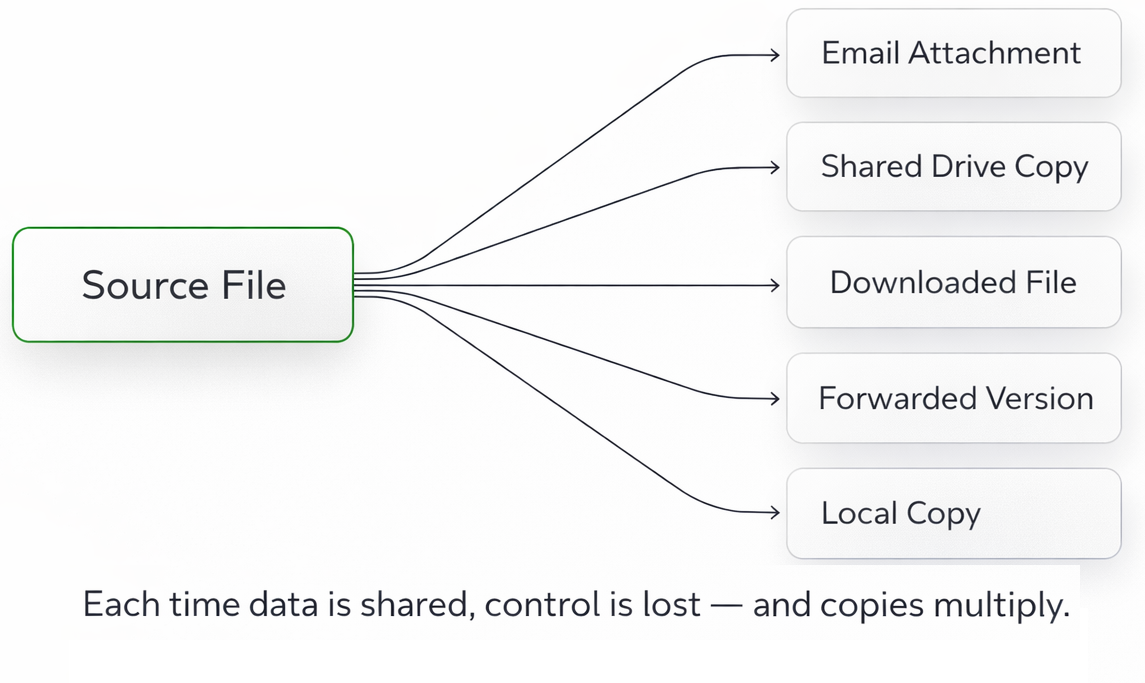
THE PROBLEMSharing data shouldn’t mean losing control.
Most businesses still share sensitive information by sending files.
Email attachments.
Shared drives.
Download links.
Every time a file is sent, control is lost.
Multiple copies are created.
Versions drift and become inconsistent.
Access can’t be reliably revoked.
There’s no clear audit of who has what.
What starts as “sharing” quickly becomes fragmentation, risk, and operational overhead
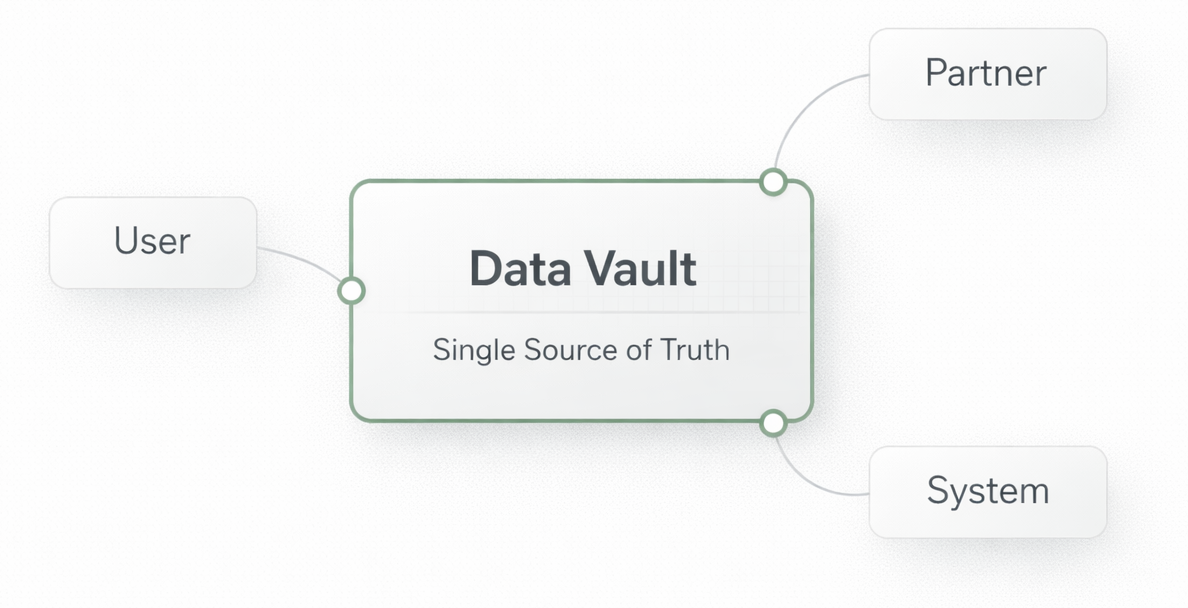
THE SOLUTIONCreate a trusted place to share sensitive data.
3 Steps Data replaces uncontrolled file sharing with private Data Vaults.
Instead of sending files into the wild, you create a controlled environment for access, review, collaboration, and, where permitted, download.
Data stays organised in one place.
Access is governed by permission.
Actions remain visible.
Each Vault can be deployed in the right jurisdiction, presented through a branded subdomain, and styled with your organisation’s logo and colours so the experience feels trusted and recognisable.
Controlled exchange. Trusted by design.
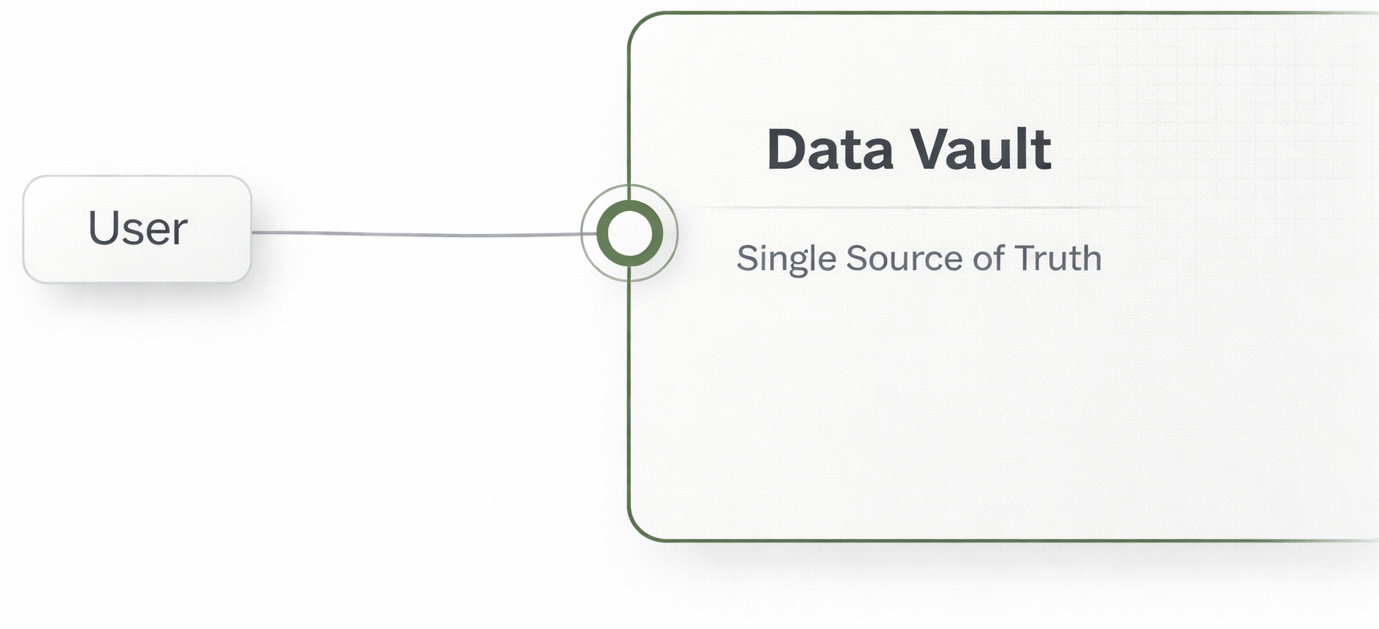
HOW DATA VAULTS WORKAccess is governed.
Actions are controlled.
Create a Data Vault for the information you need to share.
Instead of sending files, you invite people, partners, or systems into the Vault.
Permissions define what each recipient can do, whether that is viewing, contributing, or downloading where allowed.
Access can be updated or revoked at any time, without losing control of the underlying data.
The data stays controlled. Access is managed by design.
View
Edit
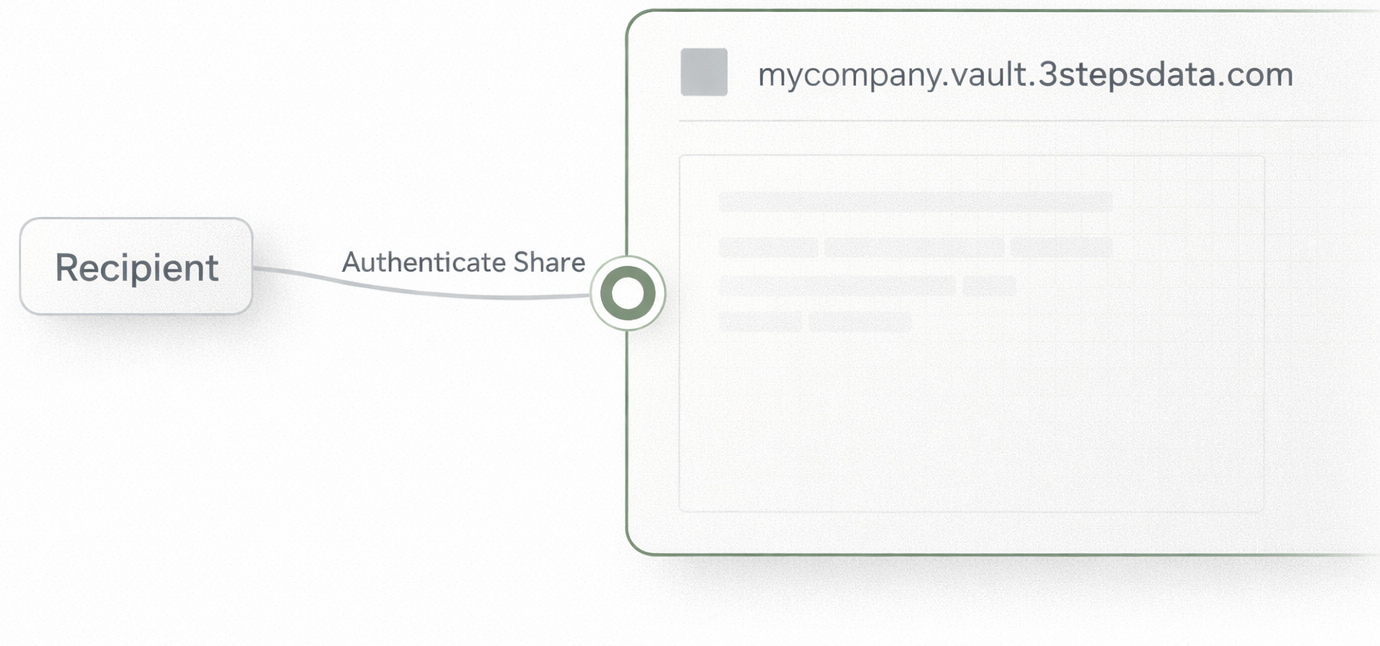
DownloadTRUST AND CONTROLKnow it’s real.
Know where it lives.
Every interaction with a Data Vault is verifiable.
Recipients can use Authenticate Share to confirm that a request or share is genuine, reducing the risk of phishing and uncertainty.
Each Vault is presented through a branded subdomain, with your organisation’s identity and visual language applied so people know exactly who they are interacting with.
You also choose where the Vault is deployed, so data is handled in the right jurisdiction from the outset.
Trust is not assumed. It’s built into every interaction.